I can no longer connect to some SFTP servers using Directory Opus (11.7 and 11.8, Windows 8.1, 64 bit).
I can still connect to some SFTP sites, but connections to two regularly used devices fail. Both are Synology NAS devices running DSM 5.1, and both are configured with custom port numbers (i.e. not port 22). I am not certain when the problems started, so this may be related to a recent update from DSM 5.0 to 5.1. It does not really seem to be a Synology problem, though, as I can still connect with WinSCP (with SCP fallback disabled) and with Putty (PSFTP). I have tried removing and reinstalling both Directory Opus and PuTTY, and clearing the relevant server fingerprints from the registry, to no effect. I have also tried a quick connection rather than the saved server configuration. It is seemingly not related to network or firewall environments: I've tried both on the same LAN as the device and over the internet, and by IP address and hostname.
FTP logging provides little additional insight for one of the servers. An unspecified error occurs after the start of key exchange, and the connection closes without retries.
[quote]Doing Diffie-Hellman key exchange
SSH: ssh_init: error during SSH connection setup 0
Connection closed[/quote]
This is with FTP logging (and debug) enabled. Enabling the advanced preferences setting for verbose logging (ftp_ssl_verbose) does not seem to log any additional information (I restarted DOpus after changing this setting as recommended).
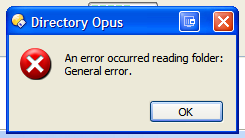
The other NAS generates a different error:
This same error can be replicated on the other NAS by disabling its setting to accept only hardware-accelerated ciphers. On or off, however, I can connect with WinSCP and PSFTP, but not Directory Opus.
I was under the impression that Directory Opus used the PuTTY code, so it is difficult to understand how it can fail where PuTTY succeeds, or why this has suddenly changed. I would be very grateful for any suggestions on how this might be fixed, or how additional diagnostic details might be logged.