These are two usercommands, to lock/unlock filesystem items (protect/unprotect from accidental deletes).
Preconditions:
- you need to be allowed to alter file and folder permissions of course
- works on NTFS drives/locations only
LockOn:
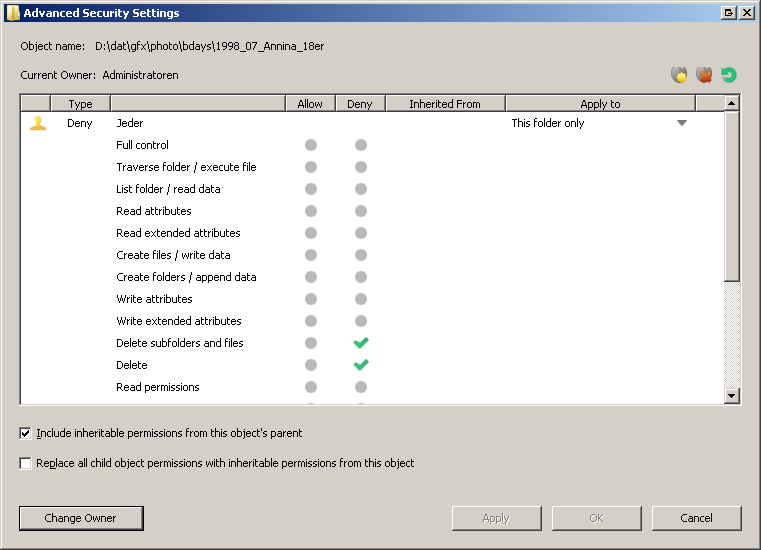
The locking is done by adding deny-delete permissions for to all selected items recursively - holding also sets the readonly attribute.
If you like to lock individual items in a folder, you need to lock the folder as well. After that, indiviual files can be locked/unlocked.
(This is because denial of delete permissions only apply if both, the actual item and its parent, share the same deny-delete-permission.)
<?xml version="1.0"?>
<button backcol="none" display="icon" textcol="none">
<label>LockOn</label>
<user_label>Enable delete/rename protection</user_label>
<icon1>#formatlock</icon1>
<function type="normal">
<instruction>@nodeselect </instruction>
<instruction>@runmode:hide</instruction>
<instruction />
<instruction>//deny delete and folder delete permission for [everyone] recursivly</instruction>
<instruction>ICacls.exe {filepath$|noterm} /deny *S-1-1-0:(DE,DC) /T /C /Q</instruction>
<instruction />
<instruction>//deny delete and folder delete permission for [everyone] recursivly, by using inheritance</instruction>
<instruction>//ICacls.exe {filepath$|noterm} /deny *S-1-1-0:(OI)(CI)(DE,DC) /T /C /Q</instruction>
<instruction />
<instruction>@keydown:shift</instruction>
<instruction>@runbatch </instruction>
<instruction>SetAttr RECURSE SETATTR r FILE={filepath$|noterm} </instruction>
</function>
</button>
LockOff:
The unlocking is done by removing all deny permissions for to all selected items recursively.
File readonly attributes will be cleared if set.
<?xml version="1.0"?>
<button backcol="none" display="icon" textcol="none">
<label>LockOff</label>
<user_label>Disable delete/rename protection</user_label>
<icon1>#format</icon1>
<function type="normal">
<instruction>@nodeselect </instruction>
<instruction>@runmode:hide</instruction>
<instruction />
<instruction>//remove all defined deny permissions of everyone recursivly</instruction>
<instruction>ICacls.exe {filepath$|noterm} /remove:d *S-1-1-0 /T /C </instruction>
<instruction />
<instruction>@runbatch </instruction>
<instruction>SetAttr RECURSE CLEARATTR r FILE={filepath$|noterm} </instruction>
</function>
</button>
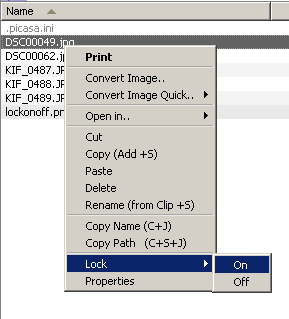
You'll run into situations where you try to make changes to items and notice you cannot because of the lock.
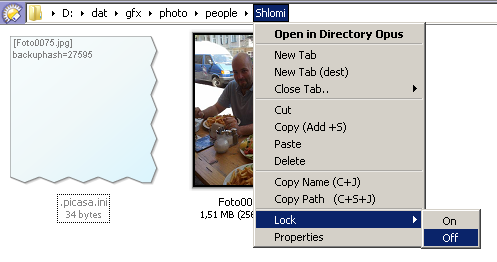
I recommend to add a menu to the "all files and folders" filetype to quickly toggle the protection from anywhere
without changing directory or loosing a current selection.
Notice:
After using "LockOn", files still can be edited and changed by you and any application, which is handy for applications which maintain tags in files e.g.
As mentioned, this is just to prevent any accidental deletes in the filesystem without notice. If you set DO to delete to the recycle-bin without confirmation e.g., it will not warn you about files being deleted which are "read only", but in case you locked your files with this, there is no chance of deleting anything anymore without a proper "access denied" popup.
Any hints on how to improve these are appreciated! o)
cya,
tbone